

Organizations face increasingly sophisticated cyber threats, making proactive security testing more important than ever. One of the most effective ways to evaluate the strength of your defenses is through a technique called penetration testing, also known as pentesting.
But what is pentesting exactly, and how does it relate to ethical hacking?
Ethical hacking is a broad discipline that involves using attacker techniques responsibly and legally to uncover weaknesses before malicious actors can exploit them. Pentesting is an application of ethical hacking. It is a structured and authorized security assessment in which professionals simulate real-world attacks to identify vulnerabilities in systems, networks, applications, and organizations.
Both ethical hacking and pentesting fall under the broader umbrella of offensive security—a proactive approach to cybersecurity that focuses on identifying and exploiting weaknesses in controlled environments in order to strengthen defenses.
This guide explains:
Whether you’re responsible for protecting systems or exploring a career in offensive security, this guide provides a structured overview of modern ethical hacking practices.
![]()
Pentesting is a structured, authorized security assessment that simulates real-world attacks to identify and exploit vulnerabilities in systems. It is a specific form of ethical hacking, which broadly involves using attacker techniques to strengthen security defenses.
In an IT security penetration test, or pentest for short, you’ll use the same tools and procedures a hacker would use in a real attack. Such a test is a kind of IT security analysis to uncover as many vulnerabilities as possible. The key difference between an IT security pentest and a real attack is the secure and controlled execution of the test. It simulates a real attack scenario and only “exploits” vulnerabilities to show the potential damage of an attack by malicious attackers. The result is a report containing an overview of all vulnerabilities found at a technical and organizational level and their potential risks, thereby revealing potential attack vectors.
From this information, you can deduce how vulnerable a system is and which areas must be improved. The elimination of security vulnerabilities is not part of the pentest but is carried out separately afterwards.
For successful implementation, the objective must be clearly formulated. In addition to the general improvement of IT security, four additional sub-goals can be derived:
Once you understand what a pentest is, it’s important to understand why organizations perform them.
A pentest always involves testing a specific scenario, which should, of course, be as realistic as possible. In contrast to other security tests, a pentest not only tests whether a vulnerability exists but also attempts to exploit that vulnerability. This test thus allows you to determine the potential damage an attacker might cause.
The biggest advantage of a pentest is that you take the perspective of an attacker. This perspective provides insights into security problems and risks that would otherwise remain hidden from you. Thus, the question in a pentest is not whether a specific system is secure, but whether and how an attacker would achieve their malicious intentions.
When assessing your system, consider the following questions:
By using the same tools and procedures an attacker would use, you can determine the extent to which the security of your systems is endangered by threats from outside and determine whether the IT security measures currently in place are sufficient.
What results from a pentest is a well-founded overview of specific security gaps and a reliable and objective assessment of the effectiveness of both technical and organizational IT security measures. Combined with an individual risk assessment, you can effectively improve IT security by deriving the most important countermeasures, that is, specific recommendations for security measures to close existing security gaps.
Pentests can vary significantly depending on the tester’s prior knowledge and the systems being evaluated. Some tests simulate an external attacker with no inside information, while others are conducted with full transparency into system architecture. Similarly, testing may focus on web applications, networks, wireless infrastructure, cloud environments, hardware, or human factors.
Understanding these variations helps organizations choose the right type of assessment for their specific risk profile.
Depending on how much prior knowledge is available to the tester, a distinction is made between three types of tests: black box, white box, and grey box. Each method has its advantages and disadvantages.
In a black-box test, no information is provided to the tester. This test, therefore, uses the same information base available to a real attacker. One advantage is that the process is quite realistic. One disadvantage is that the analysis of the IT systems to be examined requires time, which may then be lacking for the actual tests. Of course, a black-box test requires personnel who do not work directly with the systems to be tested; otherwise, too much knowledge would already exist.
In a white-box test, the tester receives all information about the target and may also use all available data. This information includes, for example, the operating systems used, which services are operated, and how the network is structured. In addition, access data to systems is sometimes used to check what damage a logged-in user can cause. One advantage is that the actual target can be tested quickly. One disadvantage is that you won’t gather any information about what data an attacker can collect from outside. At the same time, this method can lead to a kind of tunnel vision, as the systems are viewed more from the user’s perspective.
A gray-box test is a mixture of the two variants. Among other things, the tester receives access data to systems that can also be accessed externally, which might include configuring the networks without access data to provide a quick start. This step speeds up the testing process and, at the same time, ensures that no relevant components are forgotten.
In real life, these variants are often combined with each other. The first step is a rather inconspicuous and discreet black-box test, which aims to identify all relevant questions and find initial gaps. The advantage of this type of test is its realism. A more aggressive white-box test is then carried out to analyze the most important system in more detail, which in turn has the advantage that a comprehensive test can be carried out. By combining both test variants, you benefit from the advantages of both worlds.
There are many ways pentesters can try to access systems. We can’t cover them all, but here are overviews of some of the most-popular attack vectors.
When considering the security of web applications, you must take many components into account: the web server, the programming language and frameworks built on top of it, custom code, the database server, and so on. Each of these can also be a potential target for attack.
Networks connect computer systems with each other, and these computer networks can be attacked by using various hardware tools. Unencrypted data traffic in cable networks can be easily recorded or diverted. Using a local area network (LAN) adapter, as shown in the figure below, for example, you can connect between a computer and its network and simply record or redirect unencrypted data traffic. With an additional cellphone connection, you can move around the network almost unnoticed.

Today, wireless technologies are ubiquitous in almost every area—whether we control a garage door or a socket with a remote control, whether weather data is transmitted wirelessly or whether an alarm system has been implemented with wireless sensors. This type of connection is of interest to attackers since transmissions can be intercepted and manipulated (see figure below). At the same time, the physical boundary is also blurred because attacks can be carried out from outside a company building.

More and more companies/organizations are outsourcing data to the cloud. This is convenient for several reasons: Data is easily accessible on all conceivable devices (from notebooks to smartphones) and can be shared easily between different employees. Many admin tasks in maintenance are eliminated. Costs can be planned and, in some cases, are even lower than with on-premise solutions. However, this strategy comes with new security risks—you lose control of your data and put yourself at the mercy of outside vendors in more ways than one: Can you ensure that your data can’t be lost at the cloud provider (e.g., in the event of a hardware defect or fire)? Can you be sure that you have access to mission-critical data at all times, such as in the event of a network/internet failure? Is there any guarantee that the data won’t fall into unauthorized hands?
Hardware-based hacking tools represent a special category of attack tools. This special hardware can be purchased in many ordinary online stores without special permission. In some cases, this easy access makes carrying out dangerous attacks quite possible without any major know-how. For example, keyloggers have been found at newspaper offices and at police stations. Overall, the topic of hardware security has become increasingly relevant: on one hand, because more and more tools of this kind have become available, and on the other hand, because advancing digitalization has opened up more and more opportunities for hardware-based attacks.
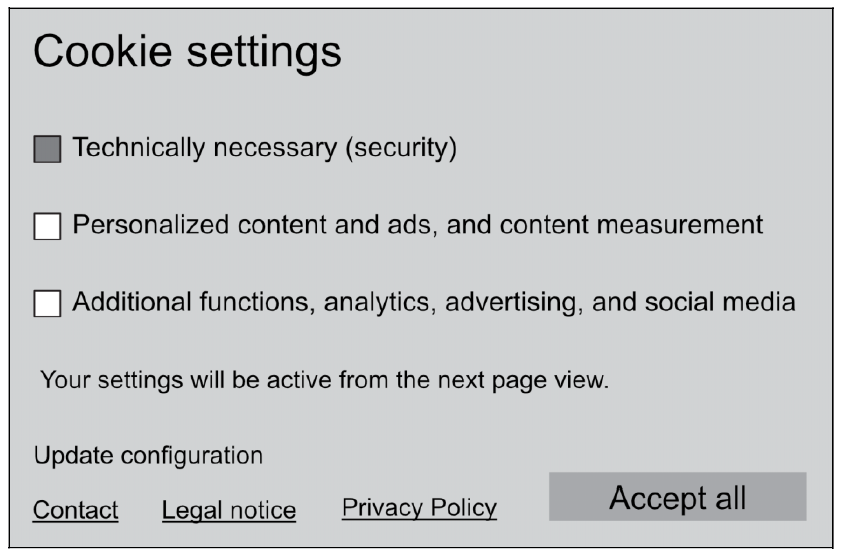
The concept of social engineering covers all methods used by cyber criminals to manipulate people into granting them access to IT systems or to carry out other actions that compromise the IT security of the environment. Social engineering involves psychological tricks to manipulate staff into carrying out specific actions or deploying confusing user interfaces, so-called dark patterns, to trick employees into carrying out certain activities that the attacker can then exploit. For example, different font sizes can create confusion among users. An attack might display the user’s preferred button as discreetly as possible, while the other button is displayed prominently. As an example, the dialog box shown in this figure obviously wants you to click Accept all.
When you plan a pentest, you must first answer the basic question of whether a pentest should be carried out on a test system or on the production system. No clear answer exists for this question; your answer always depends on the scenario.
More intensive and invasive testing can be carried out on a test system since a system crash can also be tolerated on it. However, test systems are often specially configured and therefore no longer correspond to the reality in the company.
This preliminary phase begins with defining the scope of the test as well as deciding what pentest hardware to use to test which systems. In this phase, the framework conditions are worked out including orientation (objective and depth of the test), procedure (initial situation and prior knowledge allowed), and organization (announcement and effects). As soon as all parties involved are on the same level of knowledge and all conditions have been defined, the second phase can start.
In this phase, the aim is to gather as much information as possible about the objective of the test. An important step, therefore, is for you as a tester to learn about the systems and technologies used. You must find out the names of the systems and research documentation to understand how they work. This phase is also referred to as a passive pentest since information is read or collected at this point, but no attacks are carried out yet.
You’ll use the information gained to model specific threats to which the target system could be realistically exposed. Once the possible threat scenarios have been clearly defined, the next step is to determine the specific course of action. Now, you’ll select which types of pentest hardware should be used to exploit certain potential vulnerabilities. Further, you’ll define the corresponding configurations or modify payloads for the attack scenario.
The actual safety test is carried out in this phase. All previously planned steps are now carried out with the intention of successfully attacking the target system. You connect the prepared and configured pentest hardware to the target computers or interfaces or test a wireless data connection.
Once you have fully examined the systems or reached the end of the test period, you must document the methods you employed and the checks you carried out, and then create a report that contains the vulnerabilities you have found. You should also assess these findings in terms of their damage potential and risk. You can also potentially include initial suggestions for solutions in this report, but without going into great detail.
A pentest is more of a process than a one-off action. First, a retest is necessary to check whether the vulnerabilities discovered by your first pentest have been eliminated. Second, systems are constantly changing due to updates or the addition of new components. A pentest should therefore be repeated at regular intervals.
New tests don’t need to be carried out to the same extent as an initial test but can focus on monitoring changes to the system. However, these decisions depend on how your systems are set up and connected to each other.
Although the terms are sometimes used interchangeably, pentesting and vulnerability scanning serve different purposes.
A vulnerability scan is typically an automated process that checks systems, applications, or networks for known weaknesses. Scanning tools compare configurations and software versions against databases of known vulnerabilities and generate reports listing potential issues. These scans are fast, repeatable, and useful for maintaining baseline security hygiene.
A pentest, by contrast, goes further. Instead of simply identifying potential weaknesses, pentesters actively attempt to exploit them in a controlled and authorized manner. The goal is to simulate real-world attacker behavior to determine whether vulnerabilities can actually be leveraged to gain access, escalate privileges, or move laterally within a system.
In practice, organizations often use both approaches. Vulnerability scanning helps identify common issues at scale, while pentesting evaluates how those weaknesses could be combined and exploited in realistic attack scenarios.
Red teaming is usually understood to be a form of testing in which the scope of the test is not limited to one application, but tests whether, for example, access to certain data can be obtained. The application through which the tester gains access to the data isn’t specified further so that the entire security concept is tested instead of individual applications. In most cases, the red team assessment is also regarded directly as blue team training.
In this context, the blue team is the team for the tested party that is responsible for protecting the systems. This also means that, compared to many pentests, the red team tries to hide its activities to avoid detection. Common activities include the following:
Red team assessments are a special form of testing in which several specialists from different areas may work together to achieve the previously defined goal. The assessment gives you the most realistic view of an attacker’s most likely attack path but will not evaluate all identified attack paths in detail unless otherwise agreed. Also, there is no detailed assessment of individual applications as the tester looks for the most promising attack opportunities across all applications.
The red team is also intended to train the response and knowledge of your blue team. In the best case scenario, a collaboration between the two teams is achieved, constantly improving your organization’s security and response to attacks.
The term purple teaming is interpreted in different ways. In general, the goal of purple teaming is to promote cooperation between the red team and blue team in order to constantly improve the blue team’s capabilities and be better protected from real attacks in the future. In contrast to pure red teaming, purple teaming focuses primarily on the development of the blue team.
To make the development of the blue team as structured as possible, the first step is to define the type of attacker for which the blue team should be trained and the technical means available to the blue team. Derived from this, information from the MITRE ATT&CK framework can be used to determine the usual steps taken by these groups of offenders and, based on this, a test plan can be derived. Based on this test plan, individual attack steps are specifically recreated by the red team. A subsequent analysis then determines whether existing tools and the blue team were able to detect these activities. If not, the blue team will receive all the necessary information to detect such actions in the future. In this way, the blue team is gradually introduced to the possible attack steps over several iterations and trained to recognize them and initiate appropriate countermeasures.
There are a lot of different tools that ethical hackers can use to test systems. Like with attack vectors, there are too many tools to count (and new ones are always in development). Here is a list of some of the most-popular ethical hacking tools.
Kali Linux is, in a way, the Swiss Army knife of every security and hacking professional. It’s a Linux distribution that combines a seemingly endless collection of hacking tools. Of course, you can install most of the tools in other Linux distributions as well. There are even Windows versions of some of the hacking tools. But Kali Linux has the advantage that the distribution makes many important commands for pentesting and related tasks conveniently accessible via a central menu. There is no need to spend time searching for the commands, installing them, or, if necessary, compiling them yourself.
The nmap (“network mapper”) command sends IP packets and evaluates the incoming responses to find out which IP addresses of a network segment are active, which operating systems are running on the corresponding devices, and on which ports these devices provide network services. The command thus creates the working basis for many forms of pentesting. The command is available as a package in almost all Linux distributions and can be installed easily. The nmap website also contains versions for Windows and macOS.
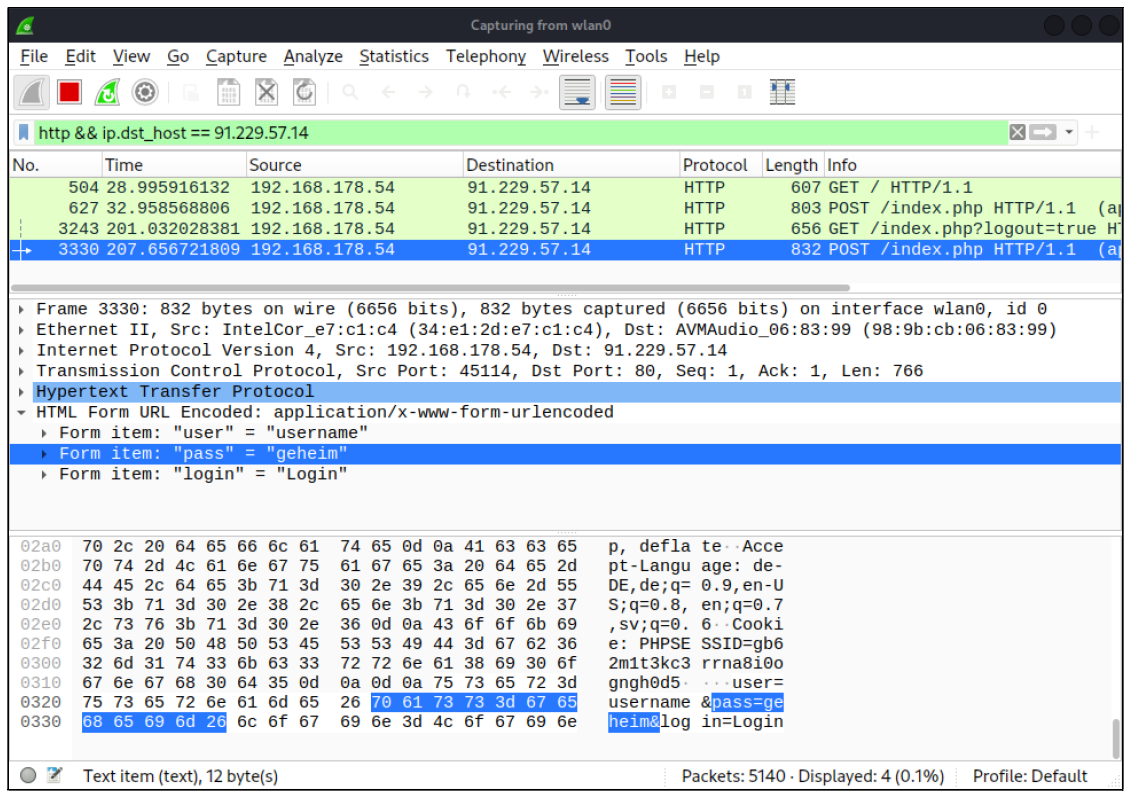
The open-source user interface Wireshark (formerly Ethereal) is a network protocol analysis program. The program tracks all network traffic on an interface, analyzes it, breaks it down into coherent pieces, and displays it “live.”
Metasploit is an open-source project whose modules help find security gaps as well as exploit them. Metasploit contains a huge collection of exploit modules. Additional modules can be used to install analysis or malicious code (a so-called payload) on the attacked computer. The best-known payload module is the Meterpreter program.
Burp Suite is a powerful tool with a graphical user interface for web application analysis. The software can basically be used free of charge; however, an important feature, the Burp Scanner, is only included in the paid version.
OWASP ZAP
The Open Web Application Security Project (OWASP) is a nonprofit organization founded in 2004 to make know-how for the development and the operation of secure web applications available publicly and independent of manufacturers. OWASP operates several subprojects. Among the best known is the Zed Attack Proxy (ZAP) software for analyzing web traffic.
hashcat is an offline password cracker that belongs to the family of graphics processing unit (GPU) crackers. The program is freely available for macOS, Windows, Linux, and Unix variants, and the source code has been disclosed.
John the Ripper (command john) is an offline CPU cracker. The program is available on Windows, Linux, and macOS. John the Ripper was developed by Alexander Peslyak (also known as, Solar Designer) and can be found here. The great advantage of John the Ripper is that numerous password algorithms are automatically recognized. If the assignment isn’t clear, you’ll receive suggestions of which algorithms might be involved.
Pentesting is a specialized role within cybersecurity that combines technical skill, analytical thinking, and a deep understanding of how systems can be attacked and defended. There isn’t a single path into the field, but most pentesters build experience in several foundational areas before focusing on offensive security.
Most pentesters start with a solid understanding of:
Understanding how systems are built and operate is essential before learning how to break them.
Before performing offensive testing, aspiring testers should understand defensive security principles, including:
A strong grasp of these fundamentals helps testers recognize weaknesses and evaluate their impact.
Pentesting skills should only be developed in legal, authorized environments. Many professionals use:
Hands-on practice is critical because pentesting is highly practical. Reading about attacks is not enough—you must understand how they are executed and detected.
Pentesting is more than exploiting systems. It also requires:
Communication skills are essential. Organizations rely on pentesters not just to identify weaknesses, but to help prioritize and address them responsibly.
Some professionals pursue certifications such as OSCP, CEH, or similar credentials to demonstrate competence. While certifications can help open doors, practical skill and documented experience often carry more weight.
Over time, pentesters may specialize in areas such as:
Pentesting requires continuous learning. Attack techniques evolve, defensive tools improve, and new technologies introduce new risks. Successful professionals stay current, practice ethically, and always operate within clearly defined legal boundaries.
Here are answers to some of the most common things people ask about ethical hacking and pentesting.
What is the difference between ethical hacking and pentesting?
Ethical hacking is a broad field that involves using hacking techniques to identify and fix security weaknesses. It can include pentesting, malware analysis, red teaming, and other proactive security activities. Pentesting is a specific, structured type of ethical hacking. It focuses on simulating real-world attacks against a defined system to identify and exploit vulnerabilities within an approved scope.
Is pentesting legal?
Pentesting is legal when it is conducted with explicit, written permission from the system owner. Without authorization, attempting to access or exploit systems can violate computer crime laws. Professional pentests always operate within a clearly defined scope and rules of engagement agreed upon before testing begins.
How often should pentesting be performed?
Most organizations conduct pentesting at least annually. Additional testing is often performed after major system changes, new deployments, or infrastructure upgrades. The frequency depends on risk level, regulatory requirements, and how quickly systems change.
What tools do pentesters use?
Pentesters use tools such as Kali Linux, Nmap, Wireshark, Metasploit, Burp Suite, and OWASP ZAP. These tools help with scanning, exploitation, traffic analysis, and vulnerability identification. However, effective pentesting relies on human expertise, not just automated tools.
How long does a pentest take?
A pentest can take anywhere from several days to several weeks, depending on the scope and complexity of the systems being tested. The timeline includes preparation, active testing, and detailed reporting of findings and remediation recommendations.
Is pentesting the same as vulnerability scanning?
No. Vulnerability scanning is typically automated and identifies known weaknesses. Pentesting goes further by actively exploiting vulnerabilities to simulate real-world attacks. Organizations often use both methods together for stronger security coverage.
In addition to the information laid out above, there are a handful of important terms you should also know:
Want to learn more about ethical hacking and pentesting? Additional information can be found in the blog posts and books listed below.
Offensive Security and Exploitation Techniques
Defensive Controls Pentesters Evaluate
Identity, Authorization, and Access Concepts
Legal and Ethical Considerations
Learn more computing from our official Learning Center.
And to continue learning even more about cybersecurity, sign up for our weekly blog recap here: